Rumored Buzz on Risk Management Enterprise
What Does Risk Management Enterprise Mean?
Table of ContentsAbout Risk Management EnterpriseThe Greatest Guide To Risk Management EnterpriseThe Greatest Guide To Risk Management Enterprise
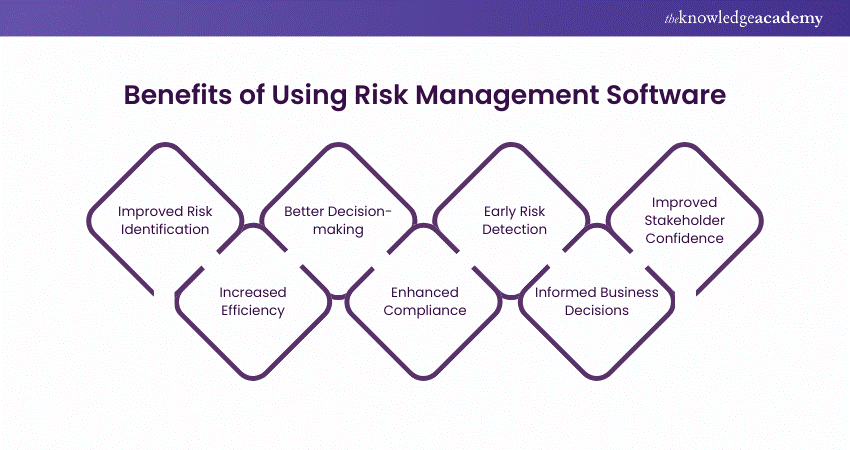
Control who can view or modify these components by setting particular gain access to rights for private customers, ensuring information safety and customized use. Permits customers to customize their interface by selecting and arranging vital information elements. Offers an individualized experience by enabling personalization of where and exactly how information aspects are shown.It permits accessibility to real-time incorporated data immediately. Facilities can make use of extensive information intelligence for quicker and extra educated decision-making.
Diligent is a risk management software program that allows maximizing performance, and boosts development. It likewise helps monitor threats with ERM software program that includes incorporated analytics and adapts to your company needs. This software program includes various valuable functions. Listed below we have actually highlighted the most essential ones. So, check them out.
An Unbiased View of Risk Management Enterprise
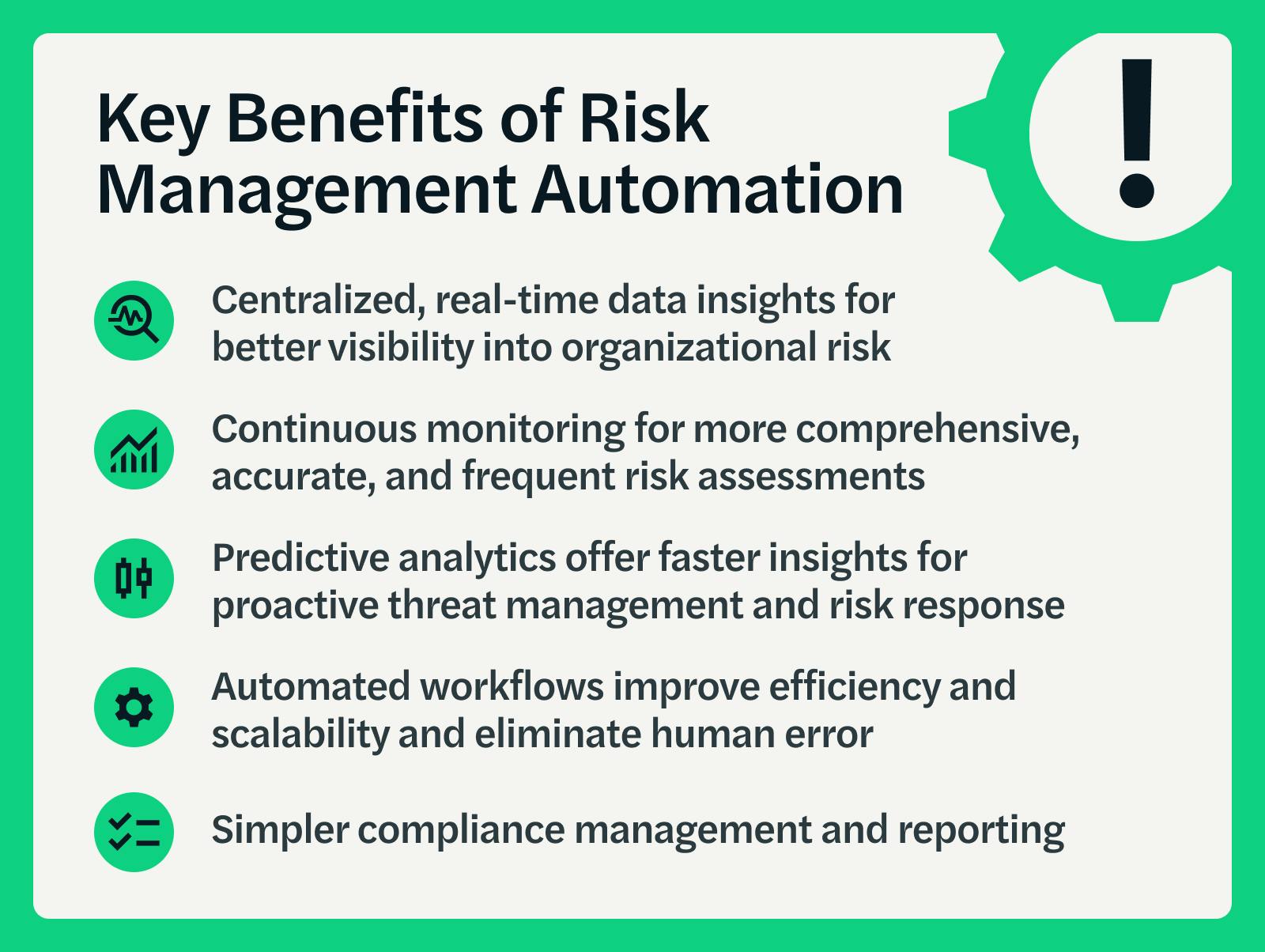
It also supplies one-click records. It offers your management and board the real-time insights they need. Streamlines the procedure of accumulating threat data from different components of the company. Risk Management Enterprise. It permits for easy personalization of records and storyboards. Provides leadership and the Get the facts board with real-time risk insights. Use ACL's sophisticated analytics to identify threat patterns and forecast threats.
This allows companies to record risk insights and red flags in the third-party supplier's safety report. Enables business to catch and document threat understandings and red flags in third-party vendor safety and security reports.
It likewise decreases risk through structured compliance and danger administration. It can assist accumulate and track all your risks in the Hyperproof threat register.
It supplies quick accessibility to necessary information and paperwork. This ensures the protection of Hyper proof instances by making it possible for multi-factor verification (MFA) using authenticator apps such as Google Authenticator, Microsoft Authenticator, or Authy.
8 Easy Facts About Risk Management Enterprise Explained
It gives top-tier protection attributes to safeguard sensitive information. This threat management software is a best tool for facilities looking to deal with unneeded concerns or dangers.
Customers can likewise utilize the AI-powered tools and pre-existing content to develop, examine, prioritize, and address his comment is here threats effectively. Streamlines the procedure of configuring and populating danger registers.